EFI REMOVAL PART 3 OF 3: FLASHROM & PASSWORD REPLACEMENT
This part of the guide is LARGELY based off of the original guide written by thaGH05T; without his generosity and creation of the GhostlyHaks community, none of what happens here would have been possible. Make sure to "buy him a beer" if you see something you like :)
The beginning steps for this tutorial take place directly after Part 1 of the tutorial since Part 2 involved hardware configuration.
PREREQUISITES
- Raspberry Pi set up with Raspbian from Part 1
- Cables and diagrams for correct connections from Part 2
- MBA EZ Flash Clip by thaGH05T OR Competitor EZ Flash Clip by RebelSimCard (for MacBook Air & later MacBook Pro models)
- Pomona (or other provider) SOIC8 SPI Flash Clip (for any applicable device)
- Ethernet Cable & access to Home Router
- 2 Amp Power Supply for Raspberry Pi
There has been some speculation as to the quality of the Competitor EZ Flash Clip, I hope I can give some insight on the device. I personally have had great success using the Competitor EZ Flash Clip. I have also encountered troubles with it. At this point I would advise one of two things: if you were lucky enough to purchase one of the original MBA EZ Flash Clips by thaGH05T then use that; for those that weren't fortunate enough to catch one by the time they sold out take advantage of the current opportunity and BUY THE COMPETITOR EZ FLASH CLIP while you still have the chance! You can find them (NO LONGER AVAILABLE FOR PURCHASE!)
STEP-BY-STEP INSTRUCTION
- Start out by logging into your Pi with:
ssh
With the default password being (without quotes) "raspberry" - Let's make sure your Raspberry Pi is ready to set up with a quick:
sudo apt-get update && sudo apt-get upgrade -y && sudo apt-get dist-upgrade -y
- Next we are going to configure our Pi so that the later steps work properly. Type the following:
sudo raspi-config
This will open up a new window that looks like the image below...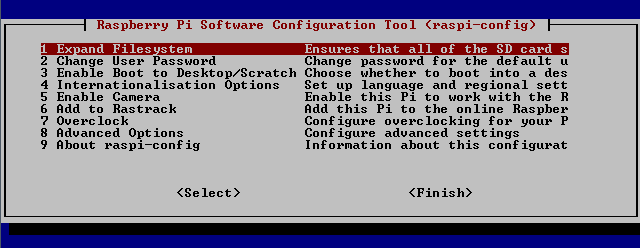
Using the arrow keys, navigate down to Advanced Options, and then in the new window choose SPI like in the picture below.
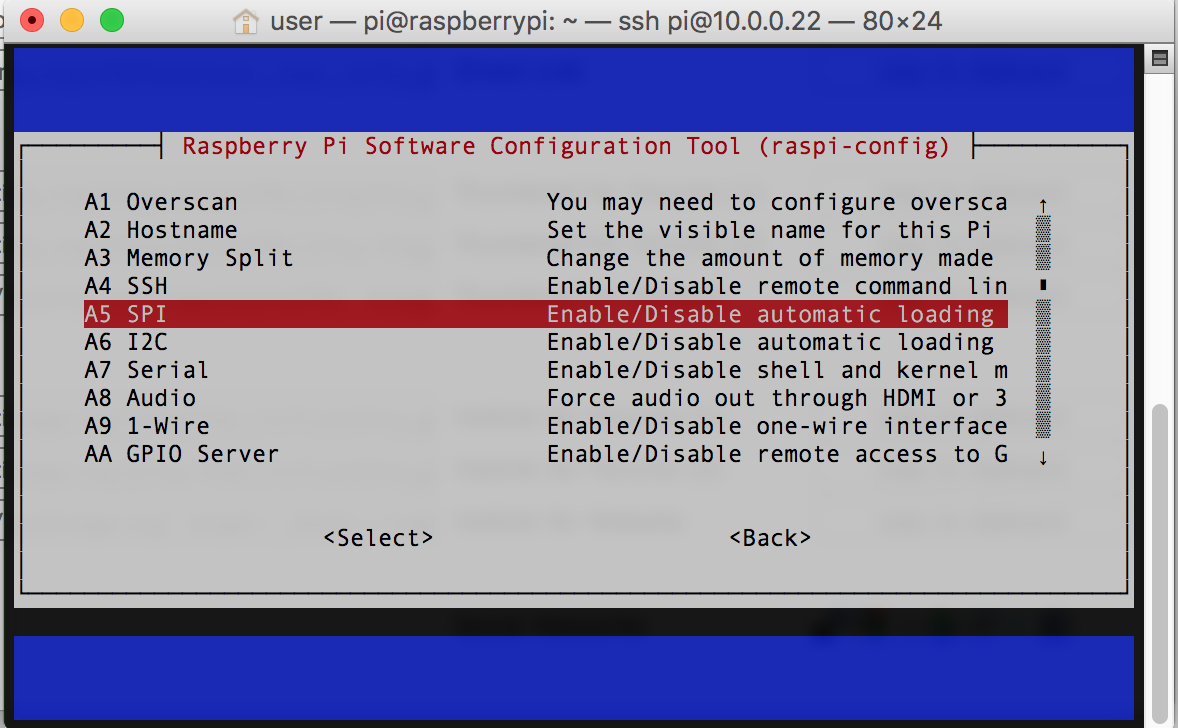
Hit Enter and make sure that you are choosing to Enable SPI. Afterwards you'll be back at the terminal.
- Now we're going to install all of the packages and resources that flashrom needs to run properly. Do so by typing the following one at a time:
sudo apt-get install pciutils
sudo apt-get install libftdi-dev
sudo apt-get install libusb-dev
sudo apt-get install libusb-1.0-0
sudo apt-get install libpci-dev
- Next we need to download, make and install Flashrom. We're going to use the command "git" to access github via the Terminal by typing:
sudo git clone https://github.com/stefanct/flashrom.git
Followed by these next commands...cd flashrom
sudo make
sudo make install
...which cd (change directory) into the Flashrom folder we previously downloaded from Github, makes the installation files, and finally installs flashrom onto our Pi. - Now we need to use the "nano" command to edit a particular file that can cause conflicts with our setup. Nano is a very handy utility that allows you to edit the contents of a file from within the Terminal. See for yourself by typing:
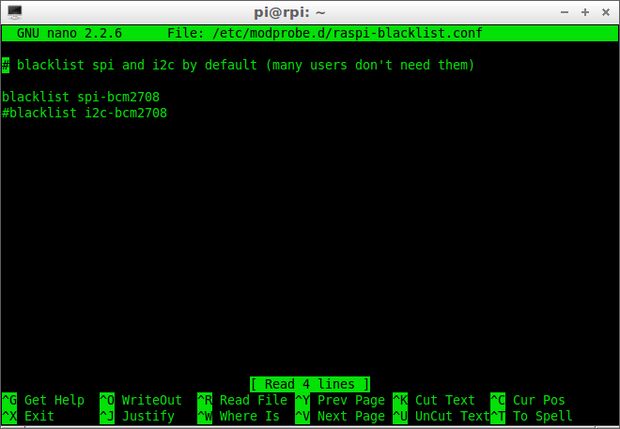
sudo nano /etc/modprobe.d/raspi-blacklist.conf
This will display a screen similar to the image below. If your screen shows nothing in the contents then you're good; typing "Ctrl+X" will return you to the command prompt. If there IS anything listed in your contents, like displayed in the below image, then look for anything that has "PCI" and, using the arrow keys to navigate, type a # at the beginning of those lines with PCI. If you look at the image you can see a perfect example of where the # is supposed to be. Once you've finished then type "Ctrl+O" to WriteOut (Save), Enter to confirm the changes, and "Ctrl+X" to return to the command prompt.
- Now we can use Flashrom! Before getting too excited, use the following information as your point of reference. These are going to be your most commonly used commands, as well as what they do and how to use them.
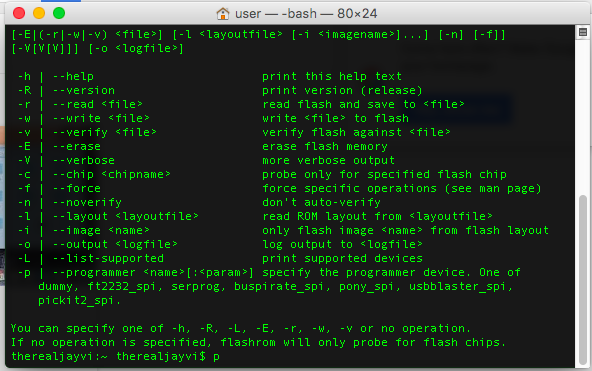
-r | --read <file> (Copies the contents of the EFI Chip to a <file> that you specify the name of)
-E | --erase (Erases the contents of the EFI Chip, make sure you definitely have a copy saved somewhere before using this)
-w | --write <file> (Writes the contents of <file> to the EFI Chip)
-c | --chip <chipname> (Oftentimes needed in order for Flashrom to perform any tasks)
-V | --verbose (As with 99% of any other Linux commands, logs more data on-screen so that you can see more of whats happening)
-v | --verify <file> (Verifies that a given <file> matches what is currently on the EFI Chip)
-p | --programmer <name>[:<param>] (Specifies which type of programmer flashrom will direct its focus upon. In our scenario we use linux_spi)
-h | --help (Prints the above help contents shown in the picture)
- Now there are some that have gotten stuck at this point when following the original tutorial by thaGH05T. It is painfully obvious that those individuals simply copy/pasted the given commands and then complained when it didn't work. A little insight into linux terminal, or most terminals for that matter. If you actually READ what the error says if you encounter one, 9/10 times directly after the error it will give you the solution to your problem. Using the original guide as an example... Hook up your Pi to the EFI Chip at this point. The following command would be the next step:
sudo flashrom -r ~/efi/read1.bin -V -p linux_spi:dev=/dev/spidev0.0
A lot of people gave up here because this command returned an error stating "/efi directory does not exist". So let's think about that one. Look at your command. sudo gives escalated permissions to use flashrom and we want it to -r read the contents of the EFI Chip into the ~/efi directory and name the file read1.bin by using our -p linux_spi:dev=/dev/spidev0.0 SPI flasher we've created and we would like the Terminal to tell us everything that happens with -V the verbose command. THINK ABOUT IT. If it's telling you that "~/efi directory does not exist" then that means flashrom is trying to put the read1.bin into a directory that "DOES NOT EXIST". Well let's continue onward by creating that directory with:
mkdir ~/efi
Now when you use the following command flashrom actually has somewhere to save the <file> you're naming read1.bin :)sudo flashrom -r ~/efi/read1.bin -V -p linux_spi:dev=/dev/spidev0.0
- "But wait therealjayvi! This gave me another error!" You're right, because we did not specify which type of -c | --chip <chipname> we are trying to crack into. BUT! If you look at the bottom of all that text that flashrom spit out at you, you'll notice that even though it doesn't know SPECIFICALLY which EFI Chip you have it connected to, it does give you all the POSSIBILITIES of what it thinks it might be! Take a look at the image below...
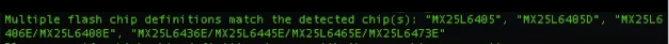
This is what Flashrom is telling you that it thinks your EFI Chip type is. Now that we have what it COULD be, let's find out what it ACTUALLY is with process of elimination. (*NOTE* THIS ENTIRE PROCESS CAN BE SKIPPED IF YOU ARE ABLE TO PHYSICALLY SEE THE EFI CHIP ON THE MOTHERBOARD AND CAN SEE THE MODEL NUMBER DISPLAYED UPON IT. IN MOST CASES YOU CANT SEE IT SINCE APPLE STARTED PUTTING THE CHIP ON THE OTHER SIDE OF THE MOTHERBOARD, SO THIS IS AN EASY WAY TO FIGURE OUT YOUR CHIP TYPE ANYWAYS!)
So in my case I would add -c MX25L6405 into my previous command so that Flashrom knows that this is what I would like for it to look for. If it doesn't work with this then I would try the next in line -c MX25L6405D and so on and so forth until you find the correct one. So to sum all of that up into one final command:
sudo flashrom -r ~/efi/read1.bin -c MX25L6405 -V -p linux_spi:dev=/dev/spidev0.0
And voila! You now have your first read of the EFI Chip. Repeat this twice more for a total of 3 different files named read1.bin, read2.bin and read3.bin before continuing to the next step.
- Now that we have 3 copies of the EFI chip, we need to verify that the copies we have came through successfully. The handy Terminal command md5sum will take care of this nicely. Using it like this...
md5sum ~/efi/read1.bin
...will return the hash value of your file. Repeat the previous command for your read2.bin and read3.bin. The point of this is to look for a consistency between the 3 hash values. If you have 3 totally different values then you cant be 100% sure which is the one to use. If all three hash values came back 100% exactly the same then it's safe to assume you had a stable read all three times. Do not continue unless you had AT LEAST 2 matching hash values, but it is advised that you have all three matching.
- Now we're faced with a situation. We have our file on the Raspberry Pi, but we need it on our main computer. Well it's a good thing we know about the scp command! SCP is almost like the brother of SSH. The difference being that SCP uses a file transfer protocol to push/pull files between two computers on a network. To do so we need to return to our host computer by typing:
exit
This will return us to the terminal of our main computer. Now remember the destination of your Raspberry Pi that we used to SSH into? We're going to combine our newly learned command scp + the destination address of our Raspberry Pi + the location of our file we want to transfer =
scp :~/efi/read1.bin ~/Desktop
So you just told scp to look for your Raspberry Pi, dig into it to the ~/efi directory we created earlier, look inside for our read1.bin file we verified, and then pull it back to our home computer and drop it into the directory ~/Desktop. Well, it WOULD do that... but first we need to enter our password for our Raspberry Pi, just like if we used SSH (default = raspberry)
- Now minimize the Terminal and check out your Desktop where you'll find the read1.bin originally from our Raspberry Pi! Now we need a way to modify it. Open up the Mac App Store and search for iHEX. Its a free utility very similar to the Windows program HxD. Once you have downloaded it, "right-click" on our read1.bin and choose Open With... and then choose to open with iHEX.
- At the top-left of iHEX click the TEXT tab instead of the HEX tab and then click Edit>Find>Find to open a search field. The string we are going to search for is the famous $SVS. Here's an example of what this will look like...
$SVS shows up twice inside of an EFI dump, and everything found in between the two is where the EFI Password is stored in encrypted hex coding. So what we want to do is nullify ALL the text found between the pair of $SVS while making sure that we REPLACE the text found within, NOT DELETE. (if using "text" then you'll replace everything with ^ and if using "hex" then you'll replace everything with FF) The reason for this is that we need our read1.bin file to end up with the EXACT same file size that it started with by the time we're finished. A good way to ensure you keep the same file size is to scroll to the very bottom of the file and take note of the position of the final character. When you're finished replacing the text between the pair of $SVS scroll to the bottom again and make sure the final character is in the exact same position before continuing.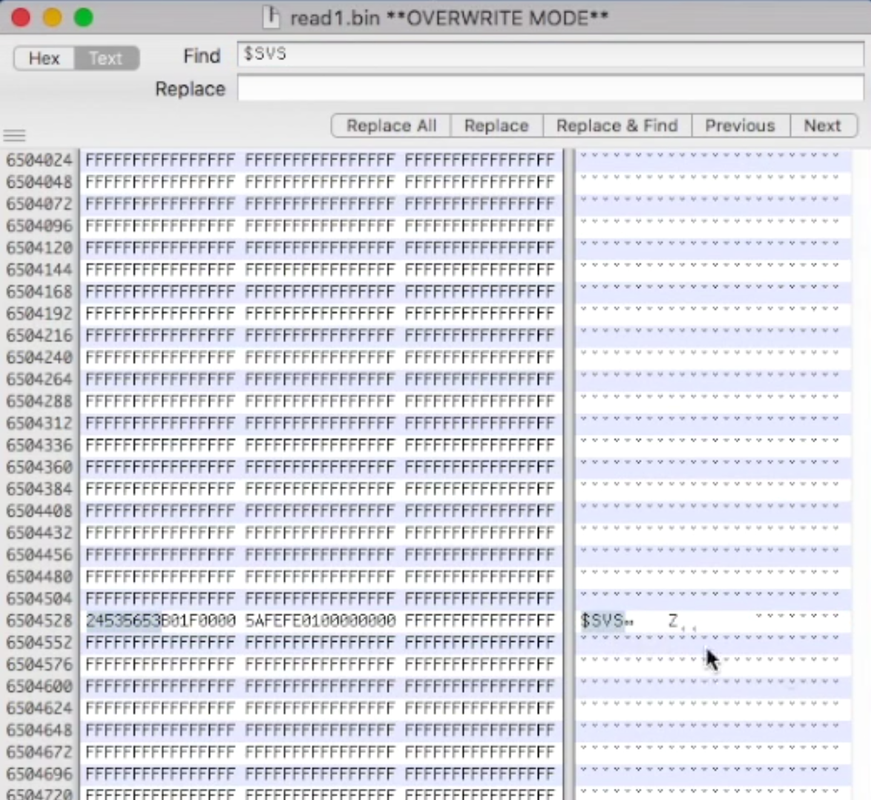
- Now that we have our newly modified read1.bin, rename it to something more noteworthy such as bypass.bin. Now we just need to reverse the order of the last few steps we covered in order to push bypass.bin to the Pi. To do so open up our trusty Terminal again and type:
scp ~/Desktop/bypass.bin :~/efi
This will put our bypass.bin back into the ~/efi directory of our Pi. Make sure to type the password for our Pi (as usual default = raspberry).
- Now we need to SSH back into our Pi with:
ssh
I shouldn't have to tell you what the password is at this point ;)
- Now that we're back at the Pi we need to -E erase our EFI Chip prior to -w writing our bypass.bin to it. So let's move forward with:
sudo flashrom -E -c MX25L6405 -V -p linux_spi:dev=/dev/spidev0.0
This will erase the contents of the EFI Chip in preparation for our -w command.
- After the EFI Chip has been erased follow up with:
sudo flashrom -w ~/efi/bypass.bin -c MX25L6405 -V -p linux_spi:dev=/dev/spidev0.0
Give it some time to complete this step and, whatever you do, DO NOT TOUCH THE PI!
- Now that we've written our bypass.bin to the EFI Chip, we need to -v verify that it has been written correctly. Type the following for peace of mind:
sudo flashrom -v ~/efi/bypass.bin -c MX25L6405 -V -p linux_spi:dev=/dev/spidev0.0
If everything has gone correctly then flashrom should prompt you with a VERIFIED! as seen in the picture below. If you did NOT get a VERIFIED! then repeat the steps to Erase, Write, then Verify until you do. If you still cant seem to get a VERIFIED! then check your connections, check that your modifications to the original read1.bin were correct and try again. If you still encounter issues then start a thread here in the forums or type a comment at the bottom of this article and we'll be more than happy to help.

- Now that you've succeeded in writing the new "password-less" .bin file back onto the chip and verified it has been written successfully, disconnect your Pi from the Mac, piece it back together, and power the thing on to test your brilliance! Upon booting the device make sure that you are holding "Command+S" so that the first thing you do is boot into Single User Mode. If you can successfully boot Single User Mode then congratulations you have done it!!! Power down the Mac and reboot but this time holding "Command+Option+R+P" while you power it on, keeping the keys held for a total of 3 reboots. Now I would recommend booting to an external OS X Installation so that you can Log In to iCloud and register the device with an Apple Account of your choosing. Otherwise the very moment it connects to the internet it's going to lock down again and you'll see the dreaded...
...all over again. If you were NOT successful in booting to Single User Mode then rinse and repeat Steps 8-18 until you get it right or make a new thread in the forums.
Some closing words for all of you that followed my guide. What you do with your own time is your own doing. I do not advocate nor promote this type of service to be done on stolen devices. People who steal things need to be reprimanded for the wrongful atrocity that they have single-handedly caused to another person. Knowledge is power. Please don't abuse it.
And as promised, here is a video example for this portion of the tutorial.
If you liked the article and would like to see many more to come then do me a favor and just shoot a small appreciation donation my way, all donations will go directly to contributing to more tutorials for the site for your learning pleasure :)

